Computer security experts have developed a system capable of guessing computer and smartphone users’ passwords in seconds by analysing the traces of heat their fingertips leave on keyboards and screens.
Researchers from the University of Glasgow developed the system, called ThermoSecure, to demonstrate how falling prices of thermal imaging cameras and rising access to machine learning are creating new risks for ‘thermal attacks.’
Thermal attacks can occur after users type their passcode on a computer keyboard, smartphone screen or ATM keypad before leaving the device unguarded.
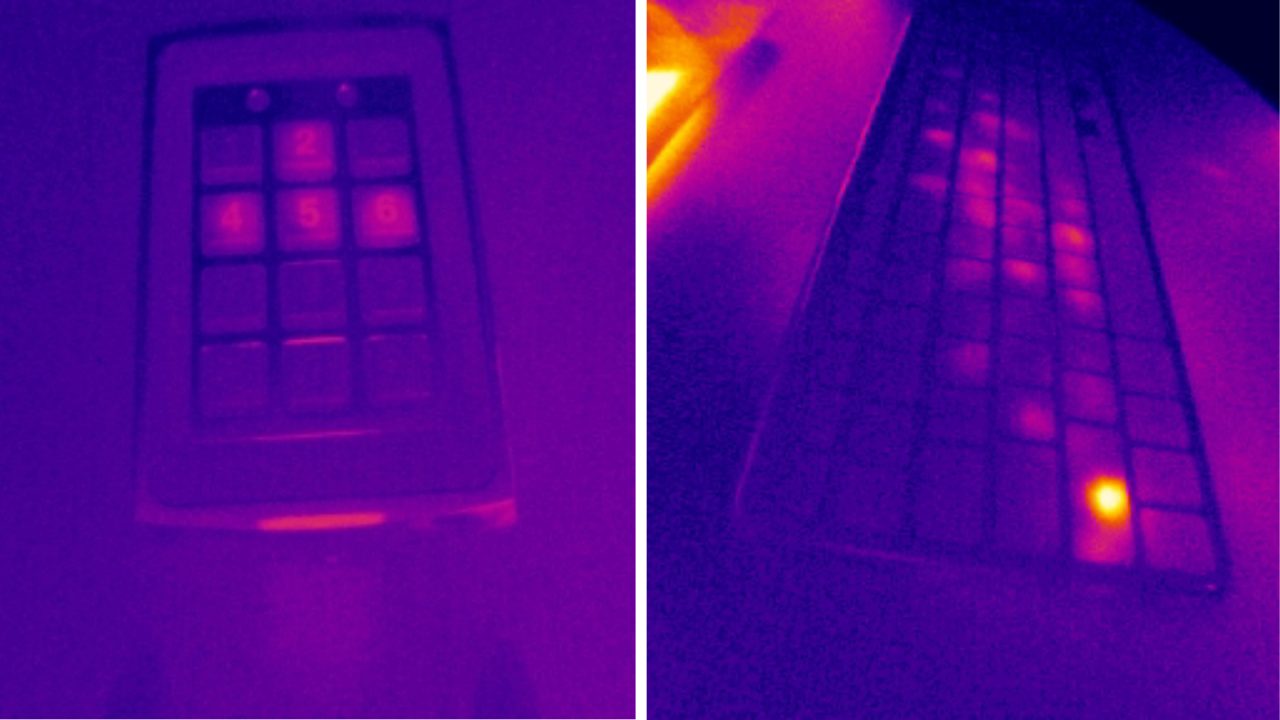
A passerby equipped with a thermal camera can take a picture that reveals the heat signature of where their fingers have touched the device.
The brighter an area appears in the thermal image, the more recently it was touched.
By measuring the intensity of the warmer areas, it was possible to determine the specific letters, numbers or symbols that make up the password and estimate the order in which they were used.

From there, attackers can try different combinations to crack users’ passwords, the team said.
Previous research by Dr Mohamed Khamis, who led the development of ThermoSecure, had demonstrated that non-experts can successfully guess passwords simply by looking carefully at thermal images taken between 30 and 60 seconds after surfaces were touched.
Dr Khamis, Norah Alotaibi and Dr John Williamson, set out to harness machine learning to make the attack process more accurate.
To do so, they took 1,500 thermal photos of recently-used keyboards from different angles.
Then, they trained an artificial intelligence model to effectively read the images and make informed guesses about the passwords from the heat signature clues.
The team found that ThermoSecure was capable of revealing 86% of passwords when thermal images are taken within 20 seconds, and 76% when within 30 seconds, dropping to 62% after 60 seconds of entry.
They also found that within 20 seconds, ThermoSecure was capable of successfully attacking even long passwords of 16 characters, with a rate of up to 67% correct attempts.
As passwords grew shorter, success rates increased – 12-symbol passwords were guessed up to 82% of the time, eight-symbol passwords up to 93% of the time, and six-symbol passwords were successful in up to 100% of attempts.

Dr Khamis, of the university’s School of Computing Science, said: “They say you need to think like a thief to catch a thief. We developed ThermoSecure by thinking carefully about how malicious actors might exploit thermal images to break into computers and smartphones.
“Access to thermal imaging cameras is more affordable than ever – they can be found for less than £200 – and machine learning is becoming increasingly accessible too. That makes it very likely that people around the world are developing systems along similar lines to ThermoSecure in order to steal passwords.
“It’s important that computer security research keeps pace with these developments to find new ways to mitigate risk, and we will continue to develop our technology to try to stay one step ahead of attackers.”
The researchers also looked at additional variables which made it easier for ThermoSecure to guess passwords.
One was the typing style of the keyboard users. ‘Hunt-and-peck’ keyboard users who type slowly tend to leave their fingers on the keys for longer, creating heat signatures which last longer than faster touch-typists.
Images taken within 30 seconds of the keyboard being touched allowed ThermoSecure to successfully guess hunt-and-peck typists’ passwords 92% of the time, but only 80% of the time for touch-typists.
Secondly, the type of material keyboards are made from can affect their ability to absorb heat, with implications for the effectiveness of thermal attacks.
The team suggests using longer passwords when possible and using other authentication methods like fingerprint or facial recognition.
“Backlit keyboards also produce more heat, making accurate thermal readings more challenging, so a backlit keyboard with PBT plastics could be inherently more secure,” Dr Khamis added.
The team’s paper, titled ‘ThermoSecure: Investigating the effectiveness of AI-driven thermal attacks on commonly used computer keyboards’, is published in the ACM Transactions on Privacy and Security.
Follow STV News on WhatsApp
Scan the QR code on your mobile device for all the latest news from around the country


 University of Glasgow
University of Glasgow